Transform Your Business with File Transfer Automation
While simple, stand-alone file transfer applications like SEP and FTP can help you get your data from point A to point B, they can be weak on secondary features. And with the amount of files businesses are dealing with today, enterprise features—like triggers, dependencies, security, and auditing—are no longer “nice-to-have” but “need-to-have.”
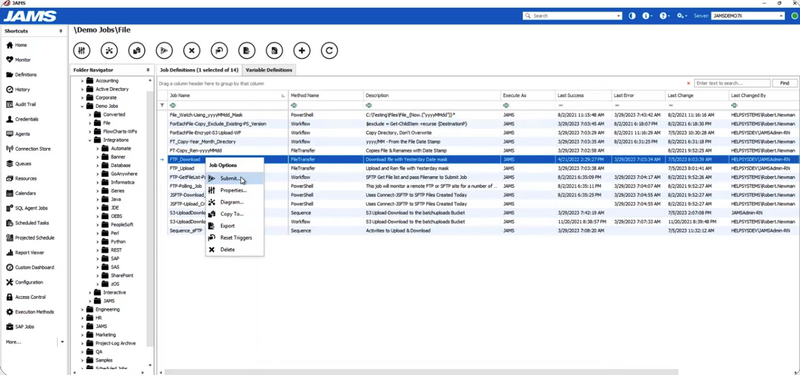
An enterprise FTP scheduler like JAMS makes managing file transfers an integrated part of your business and IT workflows. By incorporating file transfers with advanced job scheduling, you’ll be able to automate file transfers and ensure your data flows quickly, reliably, and securely.
LEARN MORE